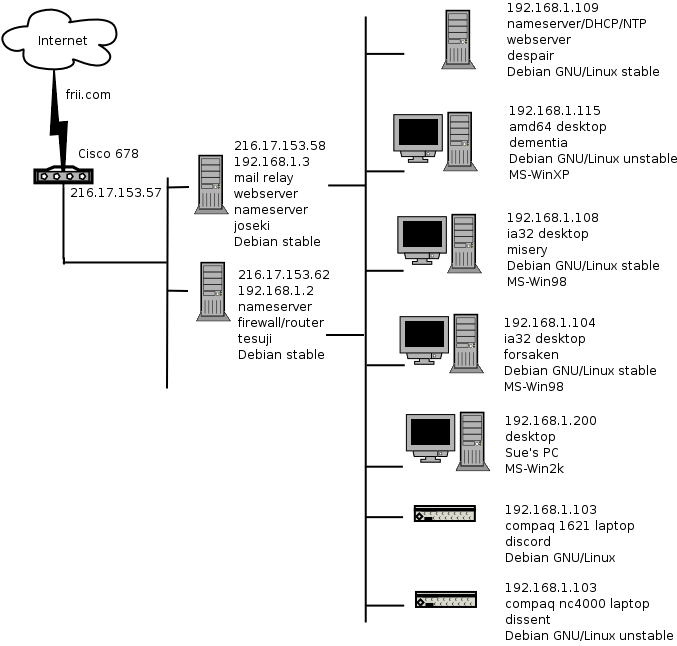
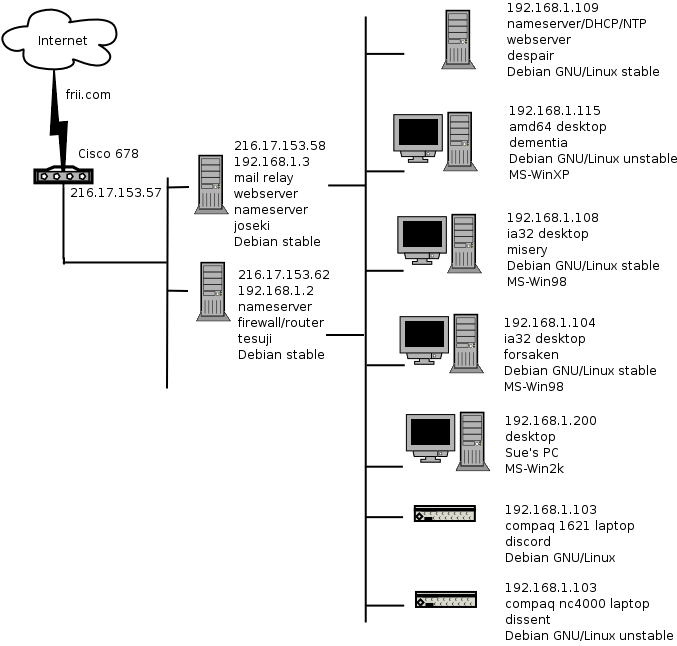
The previous Cisco 675 firmware allowed me to route a subnet but the current Cisco 678 firmware breaks this. The inability to route a subnet in the Cisco 678 CBOS v2.4.6 firmware required me to organize the network completely differently in order to work around that problem. I moved my primary firewall machine and I dual homed my primary domain serving machine. A local firewall has been installed on each system. The systems without the capability for self-hosting a firewall or that I did not trust doing so have been taken off-line.
This configuration is undesirable for a number of reasons. Among them being the loss of a DMZ. The routed subnet hangs directly behind the DSL modem with no opportunity to place a firewall between the Internet and any of the public network servers. Therefore no true DMZ exists. In particular a compromise of a machine running internet services will allow access to the private network.
A strong disadvantage of this configuration is that a system compromise affects not only the system itself but also the firewall and also the systems behind the firewall. There is no layers of security. It is really all or nothing now. In contrast using a firewall and a DMZ network means that a compromise of a host in the DMZ does not compromise the security of other hosts on the private network.
I see this configuration is a temporary configuration to keep me limping along until I can get a real DMZ configuration going again. I always implement heavy intrusion detection on any machine accessible to the Internet. I have supplemented this with even more checking. Therefore I feel safe enough that a security problem would be detected at the least and I would be able to react to the problem.